A few weeks ago, we finalized a study aiming to assess the vulnerability level of banking mobile applications in front of threats coming from users’ device environment. Here are some background information to cast light on our approach and conclusions.
First of all, some history… In every single conversation we have with banks, we are struck by the fact that they are focused on securing their Apps (and more precisely their source code) and their servers ; as well as the communication between them. Although this is mandatory, the whole security of banking applications’ users do not only rely on those two pillars. Indeed, user’s smartphone (or tablet) could expose banking applications to threats and represent a third pillar to be taken into account.
For the last 3 years, we have been drawing attention to banks on that point. All were convinced but only a few gave the appropriate priority to this topic. Even if the rise of attacks against banking applications is easily noticeable reading newspapers (Marcher).
End of last year, a bank turned to us in order to address this specific point. To bring a concrete dimension to our demonstration, we performed a vulnerability study on their own application and presented them the outcomes. Afterwards, we legitimately asked ourselves this question: what is the general assessment on banking applications in regards to this specific topic?
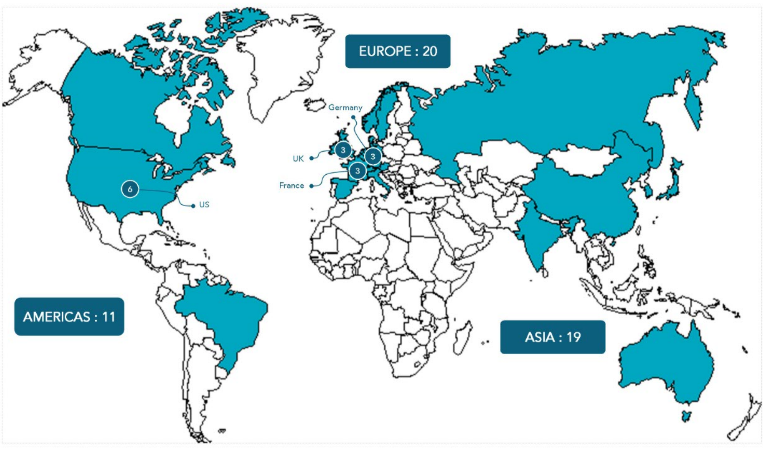
Thus, we decided to analyze the mobile banking applications of 50 banks ranked in the TOP 100 worldwide banking establishments. This subset represented 22 countries and not less than a demi-billion users.
Our analysis covered both Android and iOS using more than twenty techniques (which will be kept confidential) from sophisticated to basic ones.
Outcome of the study: 100% applications were concerned with an average number of seven techniques that went through of seven per application.
In view of these observations, we took responsibility for publishing the findings of our study with the only aim of sounding the alarm on a topic that cannot be ignored.
Obviously, this is not about judging banks (which is why we did not and will not mention any bank name). We decided to address in priority this sector as we felt it was the most urgent. However, we could have picked another one and would undoubtedly ended up with the same conclusions. The reality is that the degree of maturity of security concerns in regards to mobile (still a recent advent) is not the same as for the web for instance.
See how you can test your application security.


-1.png)
.png)
-2.png)

