Update: Following our communication with the Google Play team, the application was finally removed from the store on March 22.
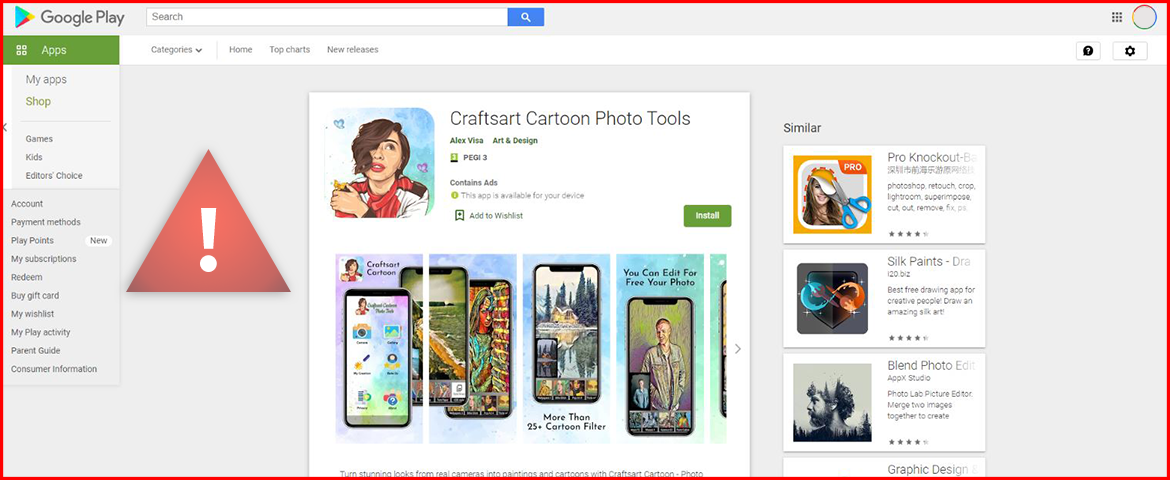
Pradeo has detected a malicious mobile application currently distributed on Google Play and installed by 100,000+ users.
The application embeds an Android trojan called Facestealer that uses social engineering to steal Facebook credentials and makes connections to a Russian server. Perpetrators leveraging the spyware have full access to victims’ Facebook accounts and all data they contain, such as credit card details, conversations, searches, etc. (see full list)
We have alerted the Google Play team of our discovery and we advise users of this app to delete it immediately.
Application’s ID
Craftsart Cartoon Photo Tools
https://play.google.com/store/apps/details?id=com.craftstoon.cartoonphoto
com.craftstoon.cartoonphoto
Version 1.0.1
100,000+ installs
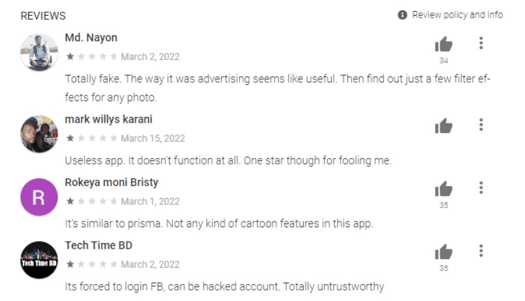
A trick to sneak malware into application stores
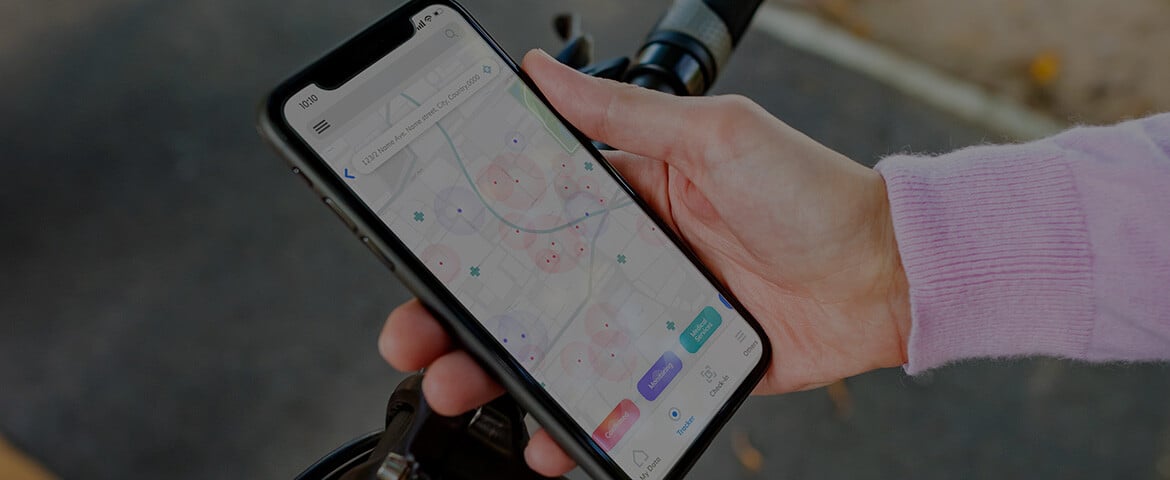
The abovementioned mobile application is distributed on Google play and third-party application stores. To reach a large public and conceal its illegal activities, it mimics the behaviors of popular legitimate photo editing applications. In fact, it has been injected with a small piece of code that easily slips under the radar of store’s safeguards.
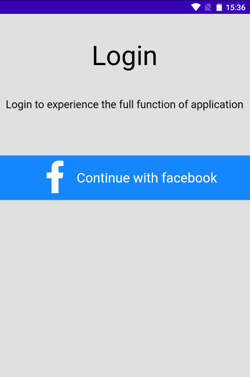
Credential collection to compromise Facebook accounts
As soon as the application is launched by users, a Facebook login page is opened and they cannot use the application if they do not log in. When they do, their username and password are automatically transmitted to cybercriminals that own the application.
Facebook credentials are used by cybercriminals to compromise accounts in multiple ways, the most common being to commit financial fraud, send phishing links and spread fake news.

Connections to a Russian domain
The application Craftsart Cartoon Photo Tools makes connections to a domain registered in Russia. Our research shows that this domain has been used for 7 years on and off, and is connected to multiple malicious mobile applications that were at some points available on Google Play and later deleted. To maintain a presence on Google Play, repackaging mobile apps is common practice for cybercriminals. Sometimes, we even observed cases in which repackaging was entirely automated.


-1.png)
-3.png)