Phishing is a hacking technique that makes a user believe that he is interacting with the interface of a trusted third party (his bank, an administration, a well-known company...) in order to exfiltrate personal information such as his password, credit card numbers, social security number, etc.
A phishing campaign is characterized, from the hacker's perspective, by the simplicity of its execution associated with the possibility to lead a large-scale attack. Although it originated in the 1990s, this type of attack is still very common today.
Until 2017, the preferred vector used for phishing was e-mail. But along the extensive use of smartphones, media have changed and attack campaigns have become more sophisticated.
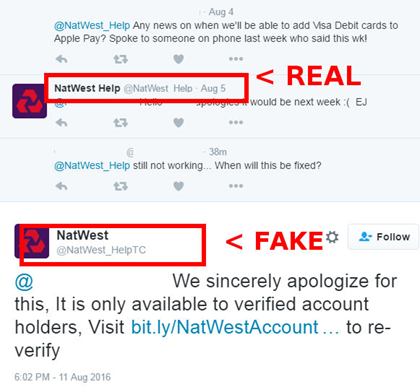
Now, the days of dodgy emails sent from meaningless addresses are over. Phishing e-mails and interfaces are almost identical to authentic ones and therefore more difficult to thwart. On the other hand, phishing attempts are no longer just about stealing personal information, but are also used to steal corporate data, since they are more valuable.
Phishing on computer VS mobile: What's the difference?
A different user behavior
The massive use of smartphones, tablets and mobile applications in our daily lives, for personal and professional purposes, turns them into essential tools that we trust and through which we are more likely to fall into traps set by hackers.
When a phishing email is opened on a PC, the user has the ability to hover the link to see where it redirects and potentially identify a malicious URL (if it does not use the imitated company’s name, which is sometimes the case). On mobile devices, however, displaying the URL is not as obvious and intuitive, making this type of attack less noticeable.
Much more attack vectors on mobile devices
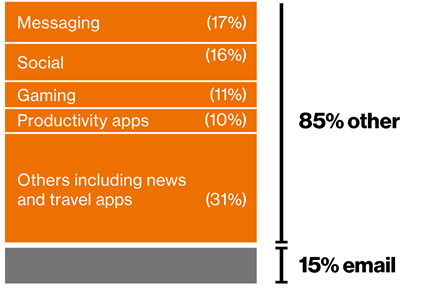
Since 2017, email is no longer the main channel for phishing campaigns, accounting for only 15% of attacks, and mobile applications have taken the top spot on the podium. With few filtering and spam detection features natively present, incoming messages are displayed regardless of their content on mobile phones.
The advent of phishing campaigns through native SMS and MMS applications on mobile devices has created a new sub-category of phishing called smishing. On other common mobile applications of various categories (social networks, games, news, travel...), hackers use messaging features.
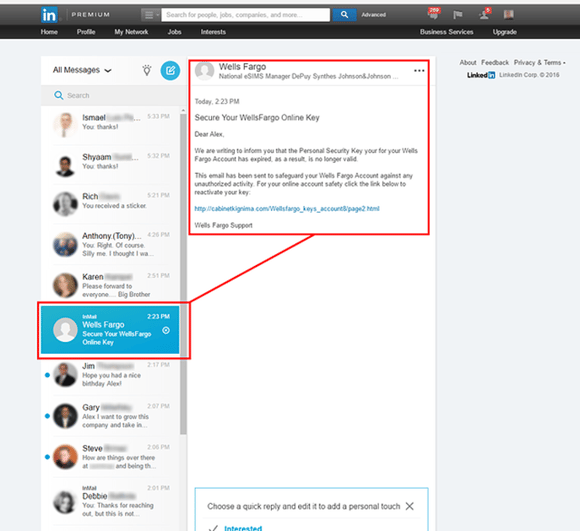
On the same principle as with emails, messages sent on mobile applications contain a short message, a call-to-action and a malicious URL. Often, they relate to common events such as an order on Amazon that can only be confirmed by updating credit card details, or an insurance policy that needs more information to be renewed.
Phishing targeting organizations: Threats and security response
By equipping employees with mobile devices or allowing the use of personal smartphones for work, organizations have become a very lucrative target for phishing campaigns.
The 2020 edition of Verizon's annual Data Breach Investigations report shows that 32% of corporate data leaks are the result of phishing and lead to disastrous consequences: bad press, legal actions, financial losses ($3.92 million on average)...
With nearly 1.5 million phishing sites created each month, 68% of which use HTTPS, threats are ubiquitous and while employees’ awareness is a good way to reduce risk, it is not entirely reliable. Verizon's study confirms this: every day, 2% of employees click on a phishing link.
Mobile devices are multiplying the channels used by hackers, and for organizations to be safe, security teams need to secure these new entry points.
Furthermore, the methods used to prevent phishing are an important factor when choosing a solution. A simple yet effective approach that redirects mobile flows raises issues of dependency and privacy. It is therefore imperative to have an approach in line with the organization's needs and constraints.
Pradeo's Mobile Threat Defense solution neutralizes all type of phishing attacks (email, SMS, applications...) to fully secure the corporate environment.


-1.png)
-1.png)
.png)

