Our team has come across an advanced mobile attack campaign that uses a phishing technique to steal victims’ credit card details and infects them with a malware that impersonates the Android Google Chrome app. The malware uses victims’ devices as a vector to send thousands of phishing SMS. Pradeo’s researchers qualified it as a Smishing trojan.
By combining an efficient phishing technique, a malware to propagate actively, and methods to bypass security solutions, this campaign is particularly dangerous. We evaluate that the speed at which it is spreading has enabled it to already target hundreds of thousands of people in the last weeks.
A new sophisticated infection mechanism
An SMS asks victims to pay custom fees to release a package delivery. When they open the link, they are first coaxed into updating their Chrome app, but the alleged update is a malware. Then, they are led to pay a small amount (usually 1 or 2 dollars at most). When they do, the cybercriminal behind this attack gets his hand on victims’ credit card details.
Independently, once installed, the fake Chrome app sends more than 2000 SMS per week from its victims’ devices, every day during 2 or 3 hours, to random phone numbers that seem to follow one another. This mechanism ensures a successful propagation of the attack campaign. To stay undetected, the malware hides on mobile devices by using the official Chrome app’s icon and name, but its package, signature and version have nothing in common with the official app.
For victims, banking fraud and massive phone bills may ensue.

Mix of techniques to bypass cybersecurity detection
The cybercriminal behind this campaign is trying hard to stay under the radar of mobile security solutions.
First, he uses his victims’ phone numbers to expedite phishing SMS, to make sure they are not blocked by messaging apps’ spam filter.
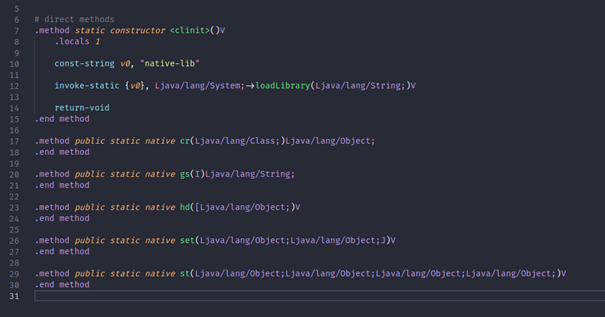
Secondly, the malware uses obfuscation techniques and calls external code to hide its malicious behaviors, hence eluding most threat detection systems.
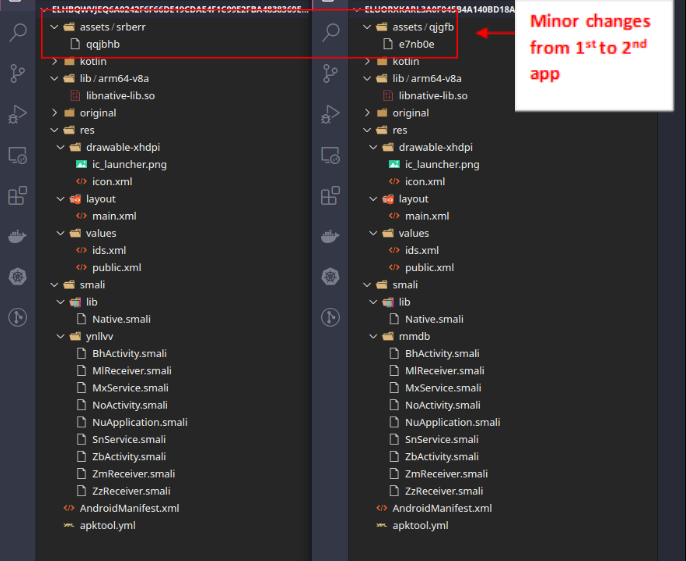
Thirdly, as soon as the app is identified and referenced by most antivirus, the cybercriminal simply repackages it with a new signature to go back under the radar.
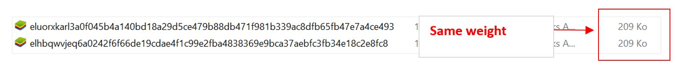
Pradeo’s engine has yet identified two fake Chrome applications as part of the campaign. When comparing both apps we have analyzed, we see that they are 99% identical, with only a few file names that seem to have been changed randomly, and on the other hand their weight is the same.
Best practices to thwart the attack
Mobile users should never provide credit card details when it is requested by an unknown sender. If uncertain of the source of the request, they should consult their package delivery with the tracking number provided by the carrier, on the official app or the website. Besides, they should exclusively download apps from official stores (Google Play on Android and the Apple store on iOS) and always update them from there.
Pradeo Security Mobile Threat Defense prevents mobile users from falling victim to this attack campaign :
- Anti-phishing that prevents browsing on malicious websites
- Malware blocking that prevents malicious and fraudulent activities