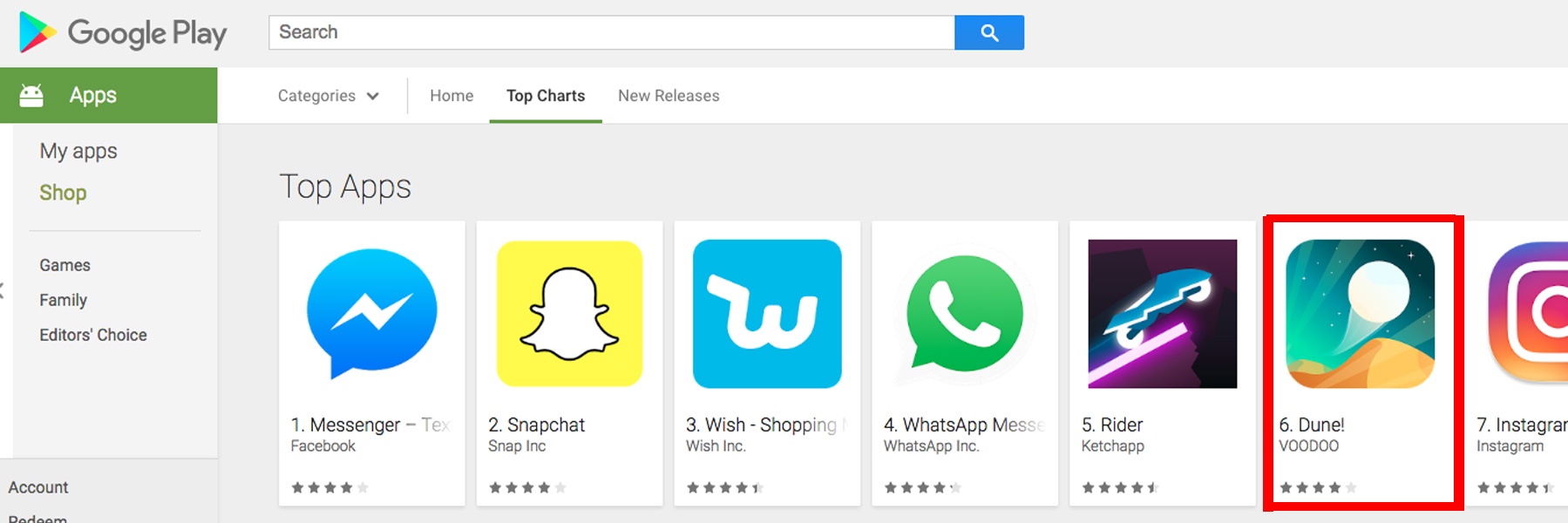
Yesterday, Pradeo’s behavioural analysis engine raised an alert about an application available on the Google Play store called “Dune!”. The app is a game that has been downloaded over 5 million times in the last few weeks and is now part of the “Top Apps” list on the Google Play store.
After looking closer to Dune! with a detailed analysis, a conclusion emerged: the app massively leaks data. Here are the main outcomes of our findings:
- Dune! geolocates users and relays their position
- Dune! leaks phone data
- Data are sent to 32 distant servers
- Dune! features 11 OWASP vulnerabilities
"Data leakage is widely seen as being one of the most worrisome threats to enterprise security as we head into 2018." says JR Raphael in a recent article for CSO.
Leakage of the user’s location
Even though it is not required for the game execution, Dune! geolocates its users. Once collected, the location data is sent to not less than 32 distant servers. Depending on the user’s type and context, like for example for Governmental employees, being able to know at any time the exact location of such category of user represents a major security issue and highlights the sensitiveness to share some time to easily that type of data.
Leakage of the device data
Dune! collects several information about the device, and sends them to a multitude of distant servers. Among the data leaked (full list at the bottom of this post), we found the operating system version which provides a clear statement of the devices’ level of vulnerability and it is often used by hackers to evaluate whether they should attack a device.
Several OWASP vulnerabilities
The OWASP Mobile Security Project classifies mobile security vulnerabilities to help developers building and maintaining secure mobile applications. Pradeo’s engine detected 11 OWASP vulnerabilities in the Dune! app, potentially putting users’ sensitive data at risk. These flaws make the app vulnerable to data leakage, denial of service and data corruption. (See full list at the bottom of this post)
More external libraries than the average
Libraries are designed for specific services (payment, analytics…) and embedded into applications. As they come from external companies, developers don’t have the hand over their source code. Very often, these libraries silently perform unnecessary actions (such as connections to unknown servers) and leak data. The Dune! app embeds 20 libraries, which is a lot more than the average. For more than half of them the only purpose is to track users and get as much information as they can about them.
Discover our analysis of the Uber app in this article: The Hidden Face of Uber
Dune! ID:
Package: io.voodoo.dune
Version : 2.2
sha1: fe6c24c9c201ebbd73a70195941f9ea2c983adaa
Device information leaked:
- Operating System version- Service provider name
- Country code for the SIM provider
- Mobile country code and network code of the SIM provider
- Kind of telephony network the device is connected to (3G, 4G, UMTS…)
- Device manufacturer
- Device commercial name
- Battery level
- Device model number
OWASP vulnerabilities detected:
| BROADCAST-ACTIVITY | The vulnerability gives permission to other applications to bypass some security access, to give direct access to potentially sensitive data. |
|
BROADCAST-PROVIDER |
The effect of this vulnerability is to give permission to any application the possibility to have direct access to sensitive data from the component. |
|
BROADCAST-SERVICE |
The vulnerability gives permission to other applications the power to start or bind the application's service. Using the flaw can lead to sensitive information leakage towards malicious apps or result in denial of service. |
|
BROADCST-RECEIVER |
The vulnerability gives permission to other applications to send malicious intent to the application. Acting on receipt of intent without validating the caller's identity may lead to sensitive data being revealed or to denial of service. |
|
URLCANONICALISATION |
Makes easier for another application to access your application data (file). Depending on the implementation of Content Provider, use of the method can lead to a directory traversal vulnerability. |
| LOG | Il est risqué de mettre en production une application qui affiche des sorties de log. Une application tierce pourra exécuter une commande et récupérer les logs contenant des informations potentiellement sensibles. |
|
IMPLICIT-INTENT |
A malicious activity or service can intercept an implicit intent and be started instead of the intended activity or service. This could result in the interception of data or in a denial of service. |
|
X.509TRUSTMANAGER |
Unsafe implementation of the interface X509TrustManager. Specifically, the implementation ignores all SSL certificate validation errors when establishing an HTTPS connection to a remote host, thereby making your app vulnerable to man-in-the-middle attacks. An attacker could read transmitted data (such as login credentials) and even change the data transmitted on the HTTPS connection. |
|
WIDGET |
It is possible for a malicious application to gain access to sensitive data through widgets, exposing the app to data leakage. |
|
POTENTIALLY-BYPASS- SSL-CONNECTION |
The implementation bypasses all SSL certificate validation errors when establishing an HTTPS connection to a remote host, thereby making your app vulnerable to man-in-the-middle attacks. An attacker could read transmitted data (such as login credentials) and even change the data transmitted on the HTTPS connection. |
|
RSA_NO_PAD |
This App uses RSA Crypto without OAEP padding. The purpose of the padding scheme is to prevent a number of attacks on RSA that only work when the encryption is performed without padding. |


-1.png)
-1.png)
-1.png)

