A few days ago, the market research firm IDC published its new report assessing worldwide Mobile Application Security Testing (MAST) vendors. Pradeo’s comprehensive expertise in the field earned it to be rewarded as a leader of the market.
If IDC is deeply exploring the mobile application security market lately, it’s no accident. Today, mobile apps are used by every organizations’ employees and clients, accessing and transmitting billions of corporate and personal information daily. Although, such a position at the center of operations comes with its share of risks, and apps are very often related to leakage, spying and cyberattacks.
Hence, organizations are in need of MAST solutions that will ensure the massive amounts of data manipulated and sent by in-house, as well as externally developed mobile applications, are correctly secure.
What are the key capabilities to look for in a MAST solution?
Many MAST solutions are available on the market, making it difficult for security heads to make a comparison. Below are the key functionalities to aim for.
Behaviors detection: Performing behavioral analysis allows to precisely identify all the actions an application is programmed to perform. It provides a clear view on what the application’s true intention is, starting point of a reliable MAST service.
Personal data manipulation identification: Under the radar data leakage is the most common application-borne threat. A MAST tool needs to identify every action performed on data, with dedicated flags on personal data specifically protected by privacy laws (GDPR, FTC Act, PIPEDA...) to ease compliance monitoring.
Code vulnerabilities detection: A MAST report needs to enlighten apps’ vulnerabilities so companies can make sure they’ll keep data safe in case of compromise attempt. To ensure the widest coverage, vulnerabilities must be tested against as many databases as possible, including the OWASP, US National and US-CERT ones.
External libraries analysis: As mobile apps nearly always embed externally developed libraries, a MAST analysis must entirely cover libraries’ code.
One tool for both Android and iOS: A mobile fleet is rarely solely Android or iOS, but usually both. Same for mobile apps. Using a tool compatible with both environments enables to centralize all testing in a unique platform.
Download our client case from the pharma industry!
What makes Pradeo Security MAST different
The Pradeo Security engine leveraged in Pradeo’s MAST service has been analyzing mobile applications for nearly 10 years, constantly improving its detection capability to keep its unparalleled level of accuracy. Here is why IDC acknowledged Pradeo as a clear leader of the MAST market.
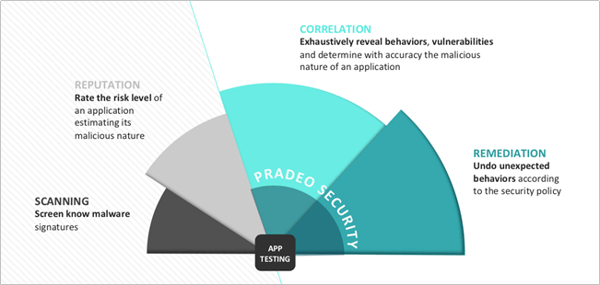
Accurate detection enabling undeniable conclusions: Unlike risk-based MAST solutions that only review apps’ permission requests to score a risk level, the Pradeo Security technology precisely identifies all the behaviors and data manipulations an application performs. Relying on this capability, Pradeo MAST tool provides the clearest conclusion on apps nature.
AI at the service of a scalable security: Pradeo Security is AI-enabled to perform its highly precise mobile app security testing on a large scale, answering large organizations need to industrialize mobile security.
Customizable security policy: In Pradeo Security, users can audit apps from a pre-defined security policy or customize one to exactly match their business context and security standards. A tailored policy enables to only flag threats that matter to the organization.
Smooth implementation of security across the entire mobile chain:
- Integration with IBM MaaS360 Unified Endpoint Management platform to ease the validation of the security level of applications prior to their distribution toward managed mobile devices.
- API to integrate security within developers’ interface, enabling a DevSecOps approach.
Automatic remediation of unwanted behaviors: Once analyzed, Pradeo Security MAST offers an exclusive functionality to repackage apps that feature unwanted behaviors. Security teams can remedy any app whose behaviors don’t comply with the security policy, to safely distribute them afterwards.
More resources about our Mobile Application Security Testing solution:







